Cloudflare is a global content delivery network (CDN) service provider used to accelerate networks and improve network performance and security services. Cloudflare uses a distributed network of nodes to provide fast and secure network services. Its services extend to over 200 countries and regions, supporting up to 200,000 websites. Cloudflare provides many excellent services, including threat protection, content optimization, anti-caching, load balancing, etc. It also offers security interception to block malicious access and attacks, protecting user content and data security.
The following operations are all foolproof operations, very simple, just click the mouse casually. But the defense effect is good, even if it exceeds millions/billions of attacks, ordinary VPS can withstand it!
Configuration
First, connect the domain name to Cloudflare, do DNS resolution well, and enable proxy status (that is, light up the orange cloud when resolving). If you have previously set up WAF (firewall rules/rate limiting rules/hosting rules/tools, as well as security page rules) according to other tutorials, please disable it, otherwise it may affect the priority of the rules set below!
Make sure there are no problems with the above, then we can start.
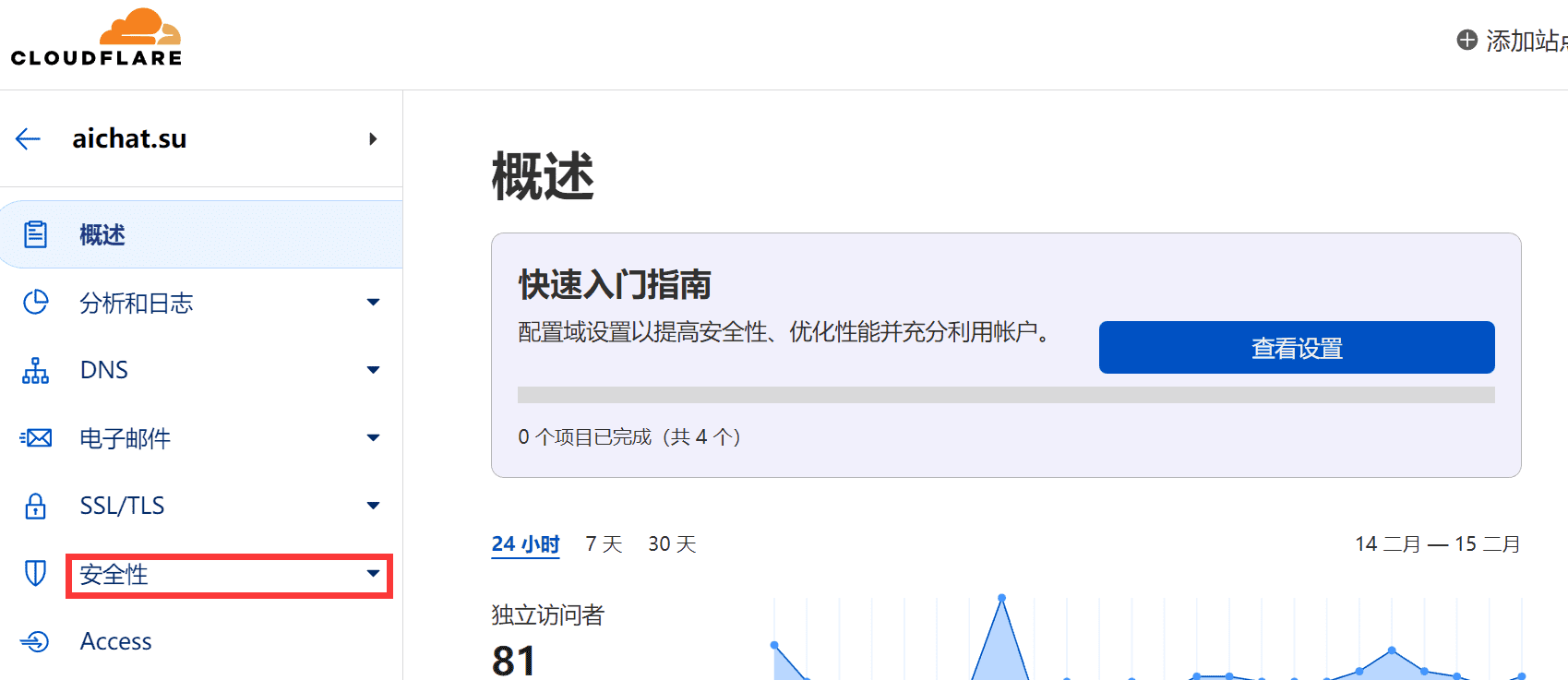
- Open the Cloudflare official website and log in, click on the website to be protected, and find security.
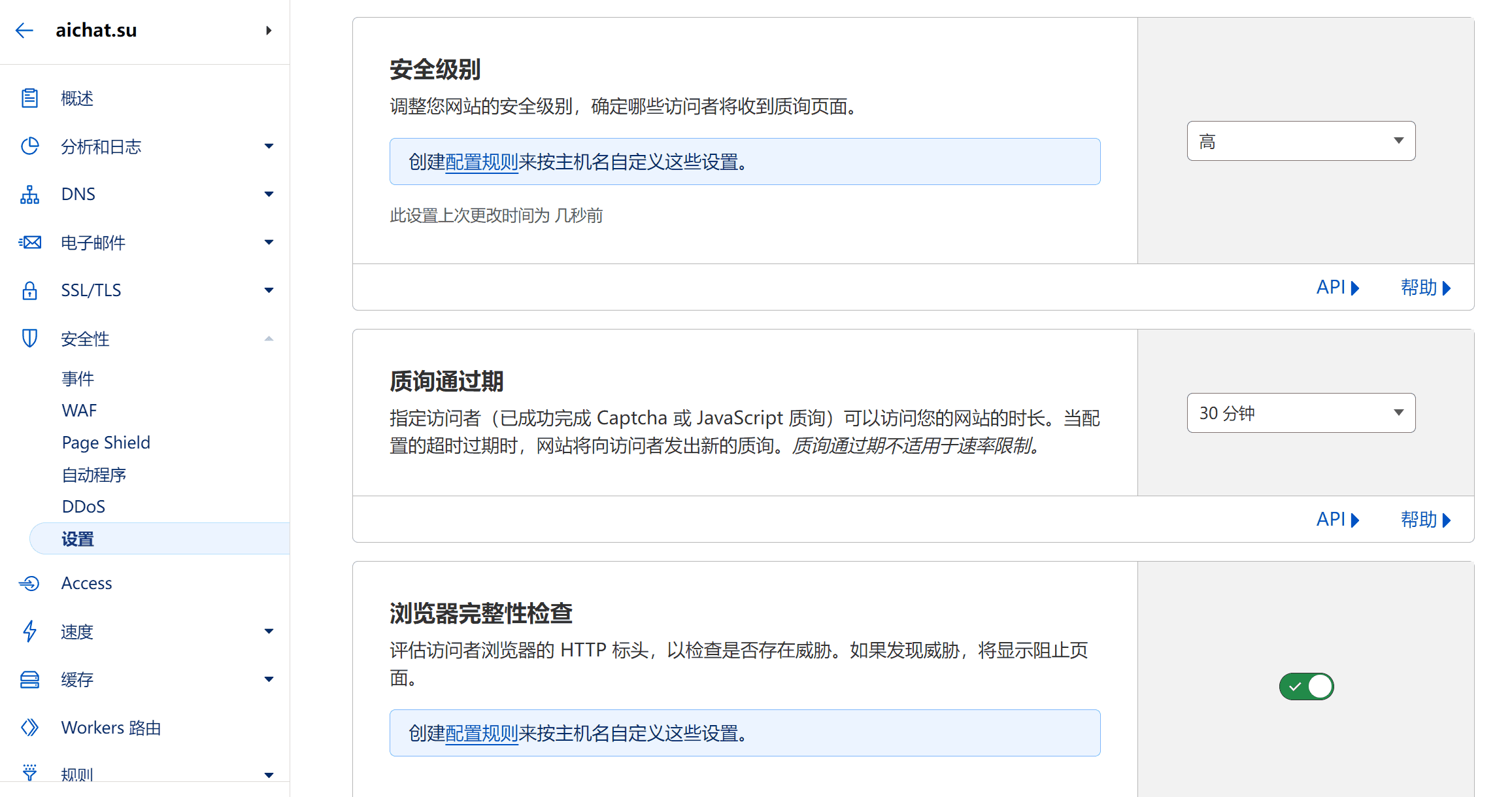
Click on settings in the security column, and set it according to the following picture. The main purpose here is to intercept those IP blacklists.
CF→Security→Settings→Set security level to: High (do not enable I'm Under Attack!, because this will require human verification for any request, wait for 5 seconds.)
Set Challenge Passage Period to: 15 minutes or 30 minutes, and set it to 5 minutes for severe cases.
Browser Integrity Check: Enable
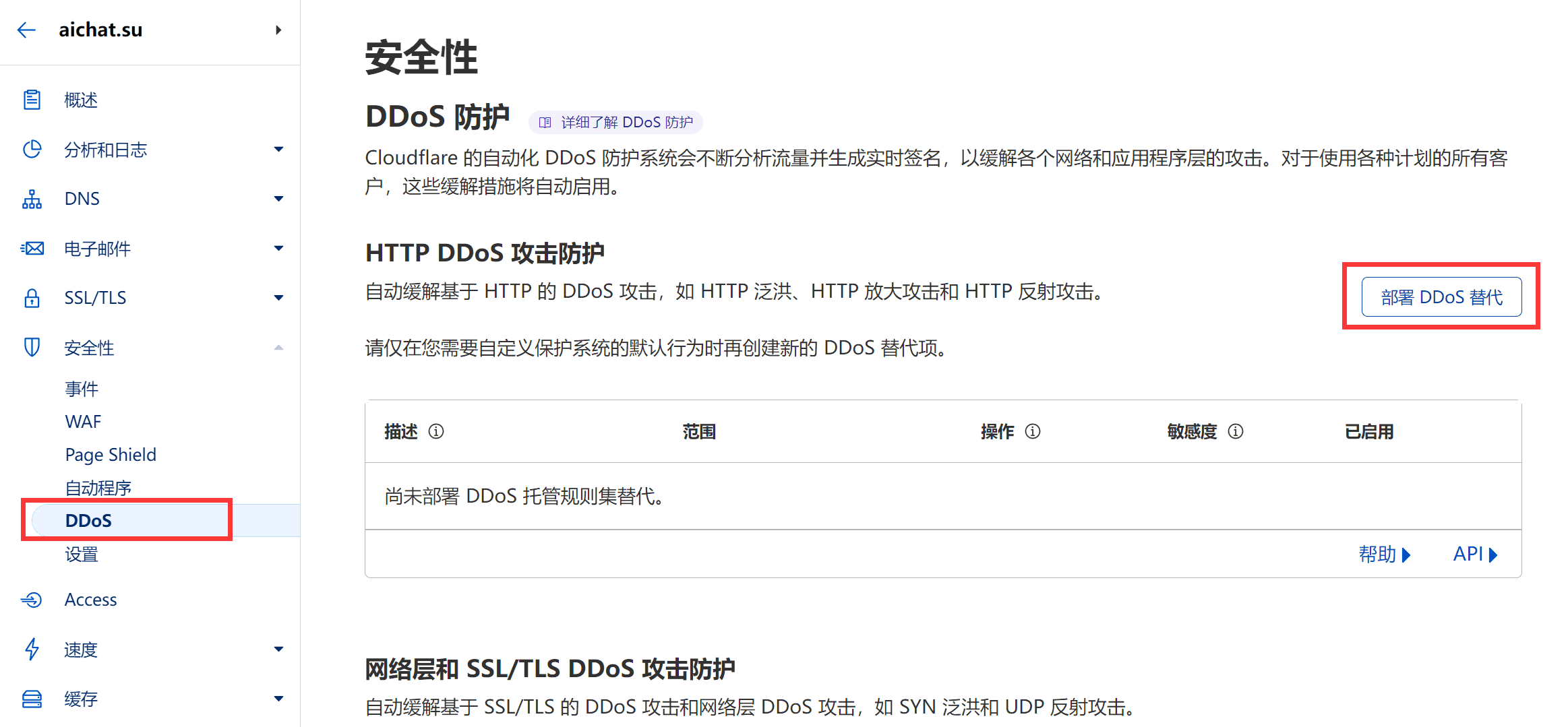
- Open Security→DDOS→HTTP DDoS Attack Protection, and click on configure on the right.
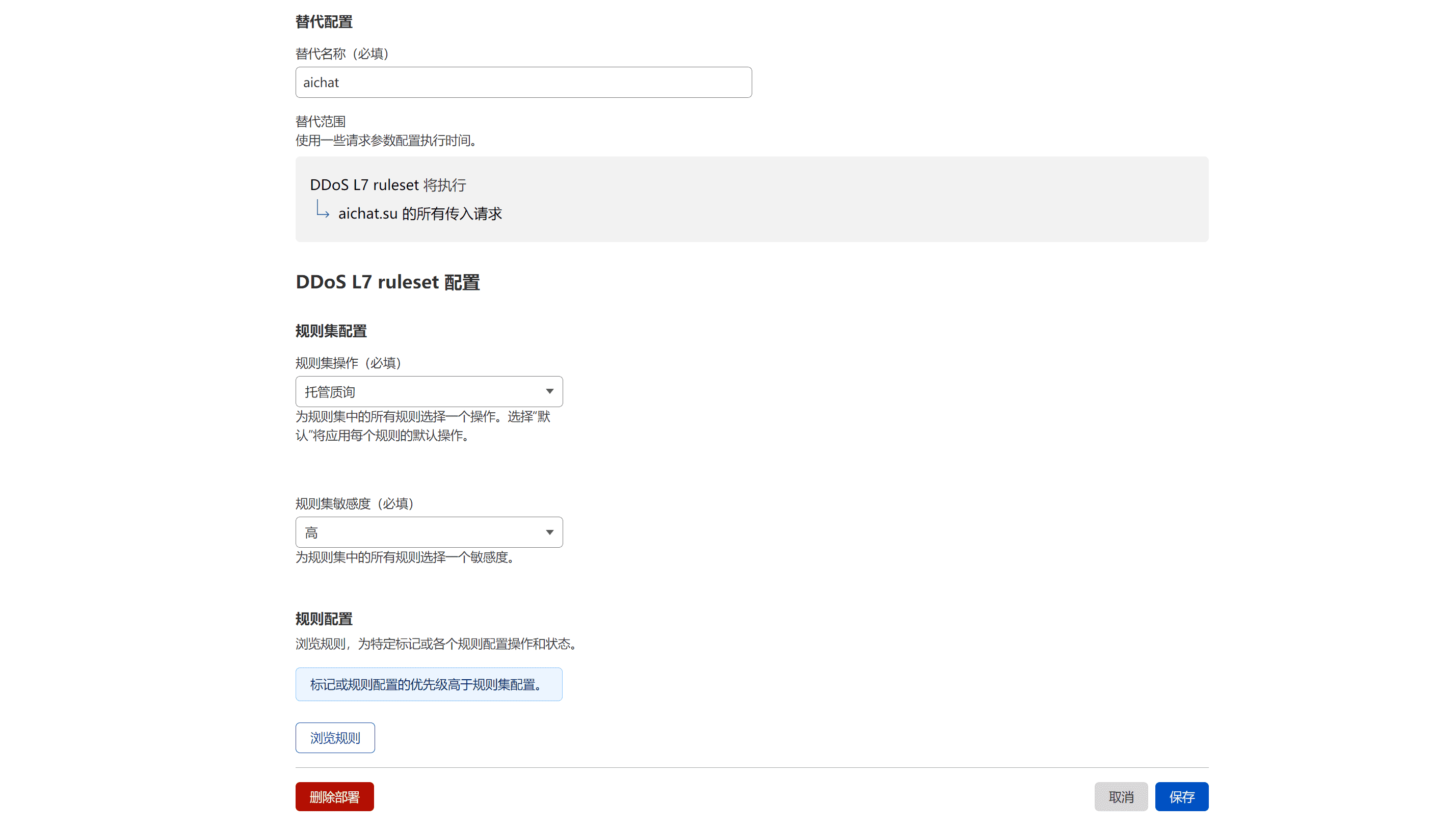
Set Alternative Name (required) to: Any name
Set Rule Set Action (required) to: Hosted Challenge or Block Directly (choose Block when under attack)
Set Rule Set Sensitivity (required) to: High
- Open Security→Bot Fight Mode: Enable Bot Fight Mode
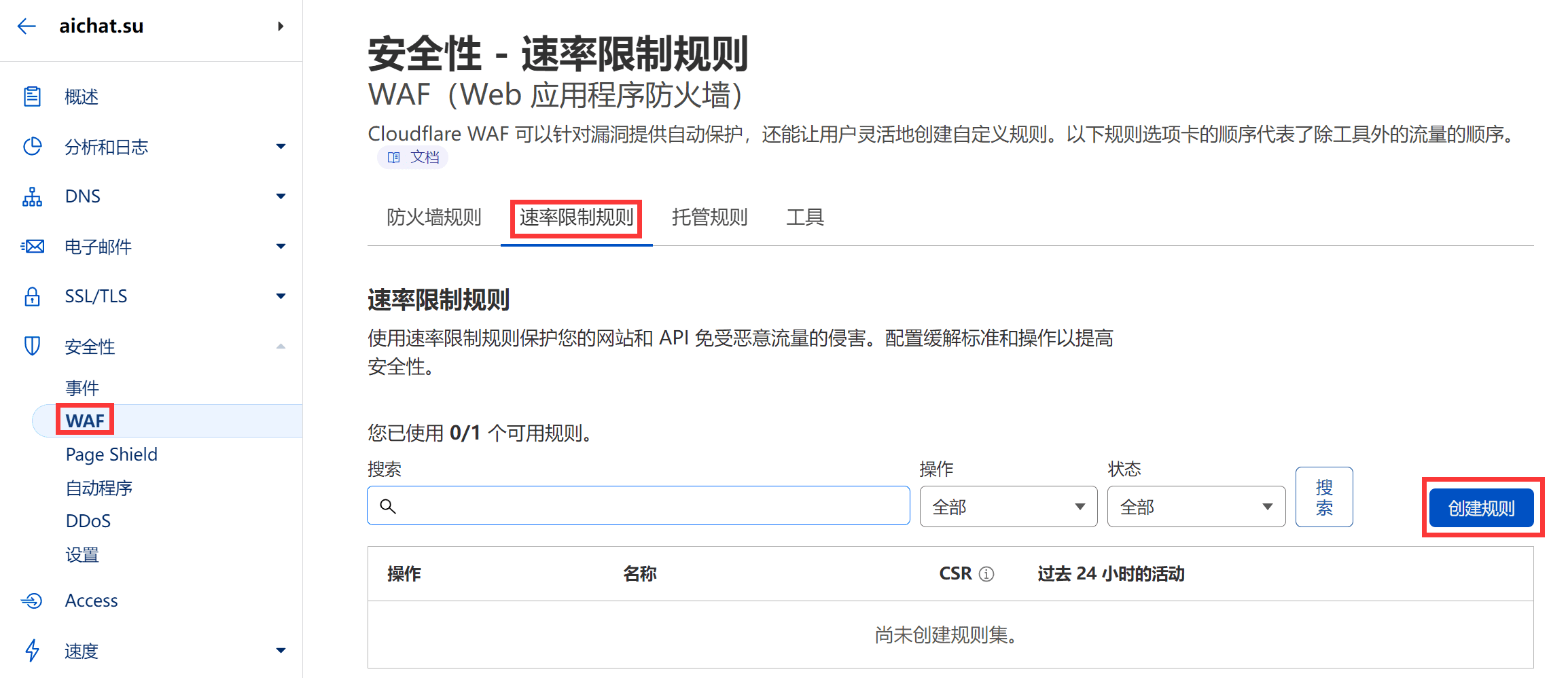
- Open Security→WAF→Rate Limiting Rules, and create a rate limiting rule.
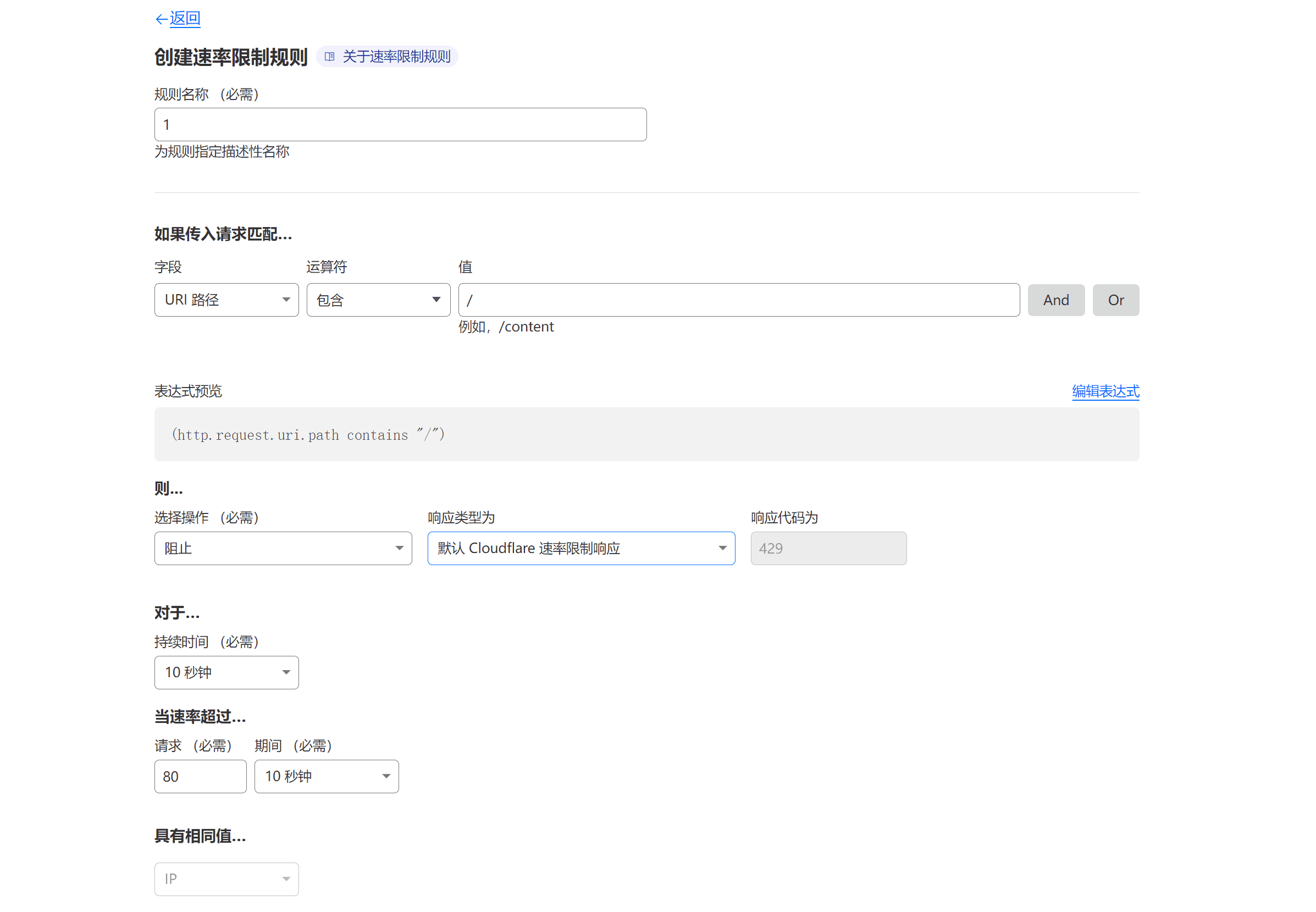
The rule is as follows:
Finally, it is recommended to fill in a request value of 35 or more for When the rate exceeds..., otherwise it will affect normal user access. For text and image blog websites, it is recommended to use 50 or more. If you are using the paid version of Cloudflare, it is recommended to use Hosted Challenge instead of blocking directly.
- Open Network→Onion Routing, and turn it off.
Finally, after setting the Cloudflare rules, wait for one or two minutes and then restart the server to disconnect existing connections.
Summary
Cloudflare is an excellent vendor that provides defense for free and does not limit user traffic. However, we must make good use of it. There are too many free and easy-to-use products that cannot withstand abuse and are canceled. I hope Cloudflare will not become the next one to be canceled!
年糕日记
此站为备份站点,最新文章请访问 oior.net